In addition to the OpenVPN: настройка OpenVPN Access Server и AWS VPC peering post – DNS settings example.
In addition to the OpenVPN: настройка OpenVPN Access Server и AWS VPC peering post – DNS settings example.
We have the ci.example.com domain, which has to be resolved to its Public IP (of the AWS EC2 instance) if it’s requested from thу Internet – or to its Private IP – if requested via a VPN connection.
To achieve this – you can use the dnsmasq service installed on the OpenVPN AS host.
Install it:
[simterm]
# apt -y install dnsmasq
[/simterm]
Create a /etc/dnsmasq.hosts file with hardcoded Private IP for necessary services:
10.0.5.10 ci.example.com 172.31.36.107 nexus-repo.example.com 10.0.3.105 rabbitadmin-production.example.com 10.0.1.6 monitor.example.com
Next – update /etc/dnsmasq.conf file and add the addn-hosts option so it will look like next:
listen-address=127.0.0.1 listen-address=10.0.10.4 bind-interfaces log-queries addn-hosts=/etc/dnsmasq.hosts
Restart the dnsmasq service:
[simterm]
root@openvpnas2:~# service dnsmasq restart
[/simterm]
Check locally:
[simterm]
root@openvpnas2:~# dig @localhost ci.example.com +short 10.0.5.10
[/simterm]
Good.
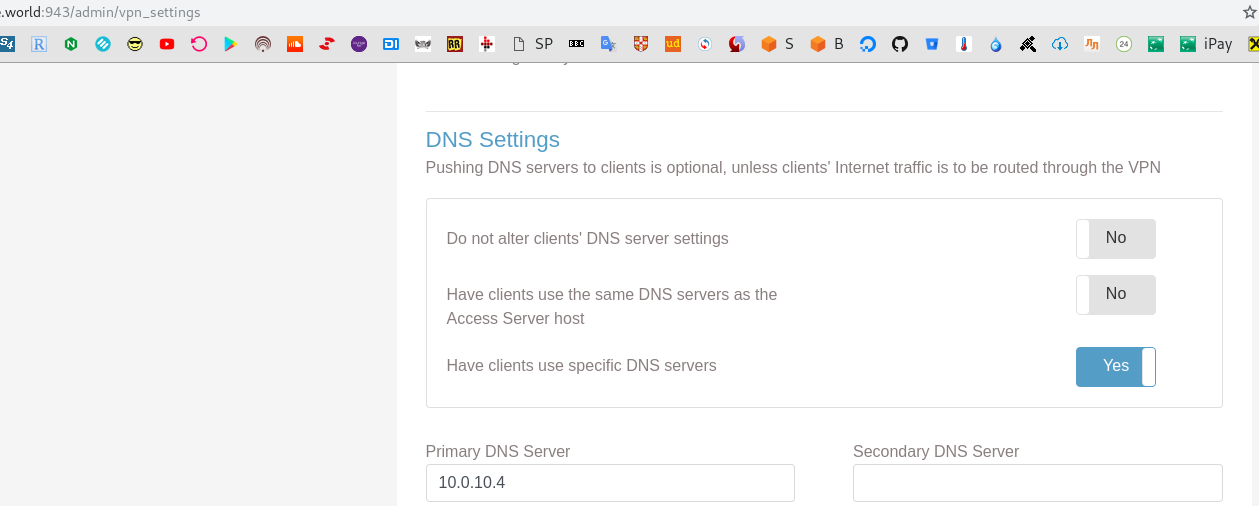
Now go to your OpenVPN’s admin page => VPN Settings and set the Have clients use specific DNS servers to Yes:
In the Primary DNS Server filed set your EC2’s Private IP where is your OpenVPN server running.
Restart your VPN connection on a workstation:
[simterm]
$ sudo openvpn --config vpnroot-client.ovpn ... Fri Feb 22 16:53:58 2019 /usr/bin/ip link set dev tun0 up mtu 1500 Fri Feb 22 16:53:58 2019 /usr/bin/ip addr add dev tun0 172.27.240.25/20 broadcast 172.27.255.255 Fri Feb 22 16:53:58 2019 /etc/openvpn/update-resolv-conf tun0 1500 1553 172.27.240.25 255.255.240.0 init dhcp-option DNS 10.0.10.4 ...
[/simterm]
Check local resolv.conf:
[simterm]
$ cat /etc/resolv.conf # Generated by resolvconf nameserver 10.0.10.4
[/simterm]
Check DNS resolution:
[simterm]
$ dig ci.example.com +short 10.0.5.10
[/simterm]
And any other:
[simterm]
$ dig google.com +short 74.125.193.100 74.125.193.101 74.125.193.102
[/simterm]
Done.
![]()