As a follow-up to the SSO, Okta, and SAML.
As a follow-up to the SSO, Okta, and SAML.
We already did everything for our Jenkins (see the Jenkins: SAML, Okta, user groups, and Role-Based Security plugin post) – now it’s time to do the same thing with our Github organization.
The idea is the same as for the Jenkins’ setup: keep all users in the Okta, during Github’s (our Service provider, SP) login – it has to ask our Identity Provider, IDP (Okta this case) to authenticate this user using SAML.
Let’s use the Okta Github Enterprise Cloud – Organization application.
Documentation:
- How to Configure SAML 2.0 for GitHub Enterprise Cloud – Organization
- About authentication with SAML single sign-on
I didn’t found yet how to realize the Groups to be passed from an Okta user’s account to Github, but I hope this is can be done.
Contents
Trial Github Enterprise Cloud – Organization
To have an ability to use SAML in a Github’s organization need to have the Github Enterprise Cloud – Organization.
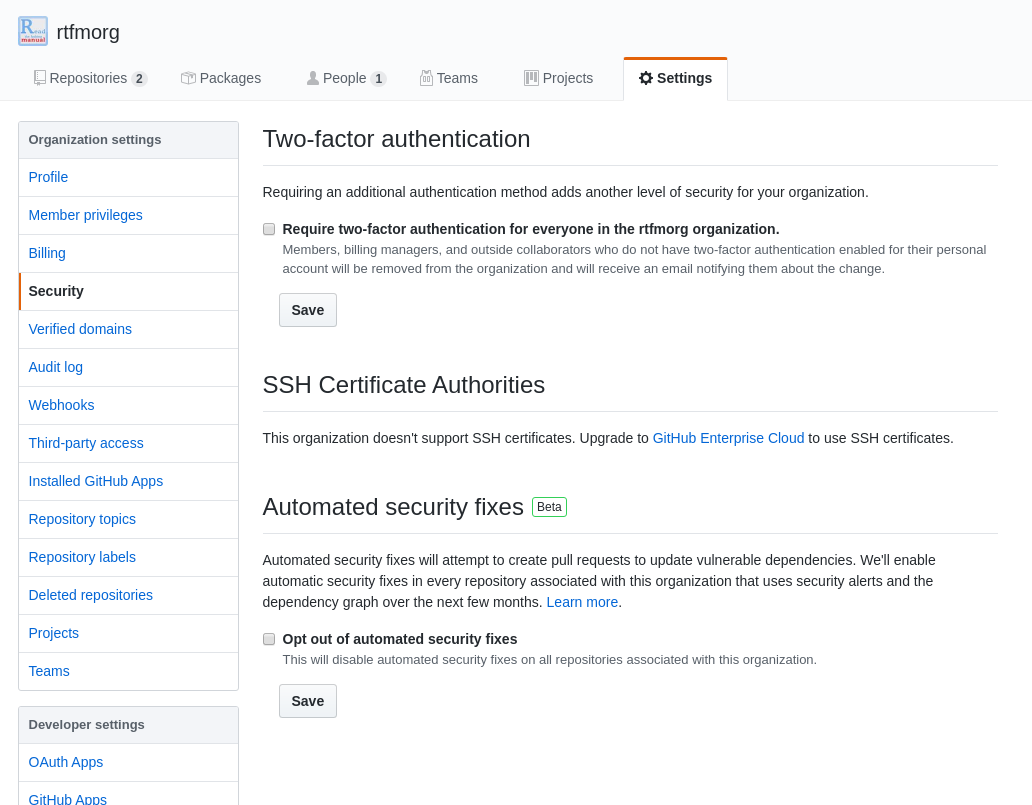
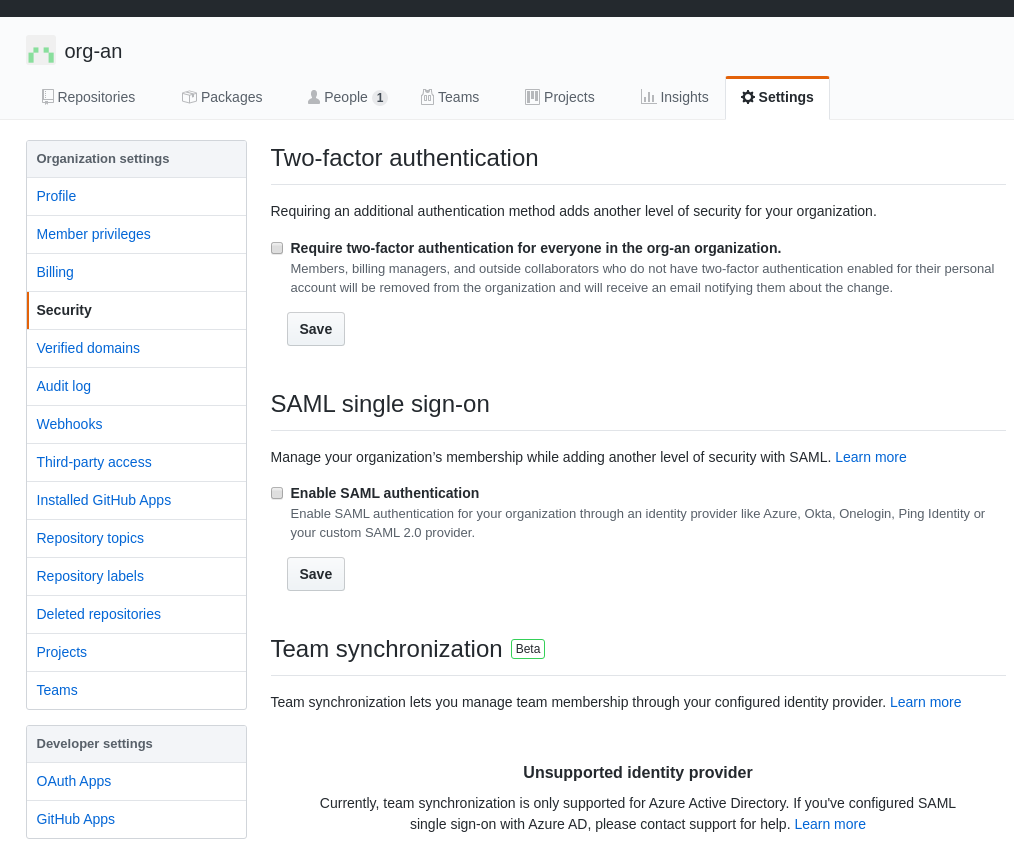
Go to your Github’s Organization, Settings > Security:
Now there is no SAML available.
For the testing purpose let’s create a new Github Organization with the Enterprise Trial subscription.
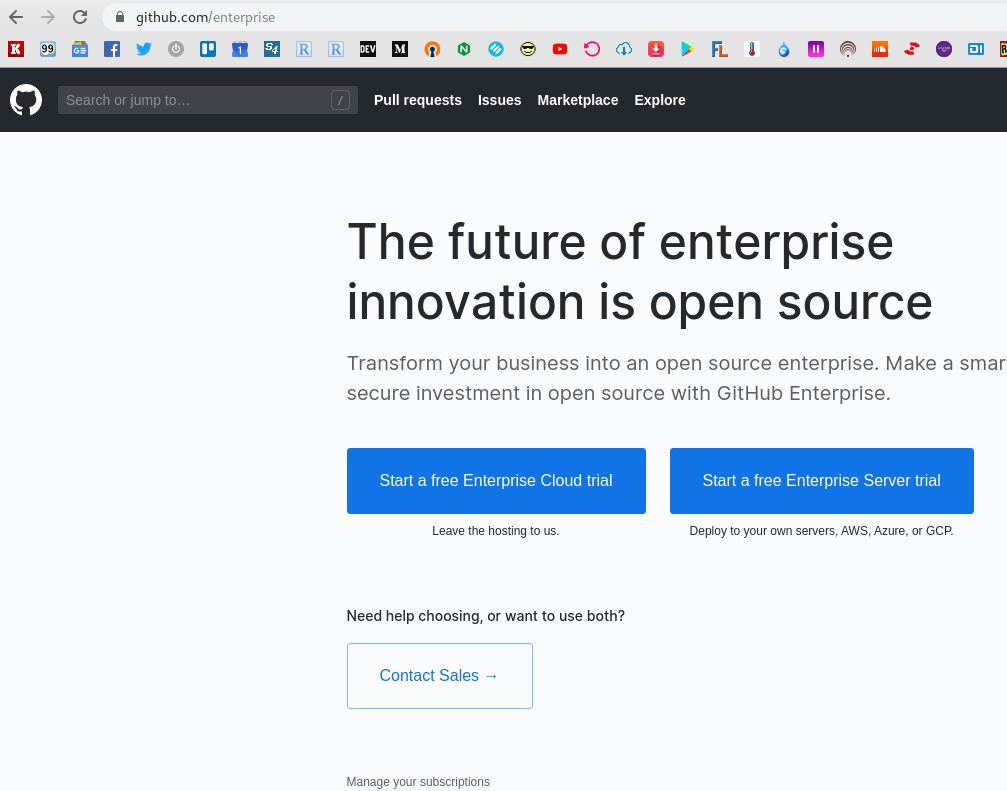
Go to the GitHub Enterprise Cloud:
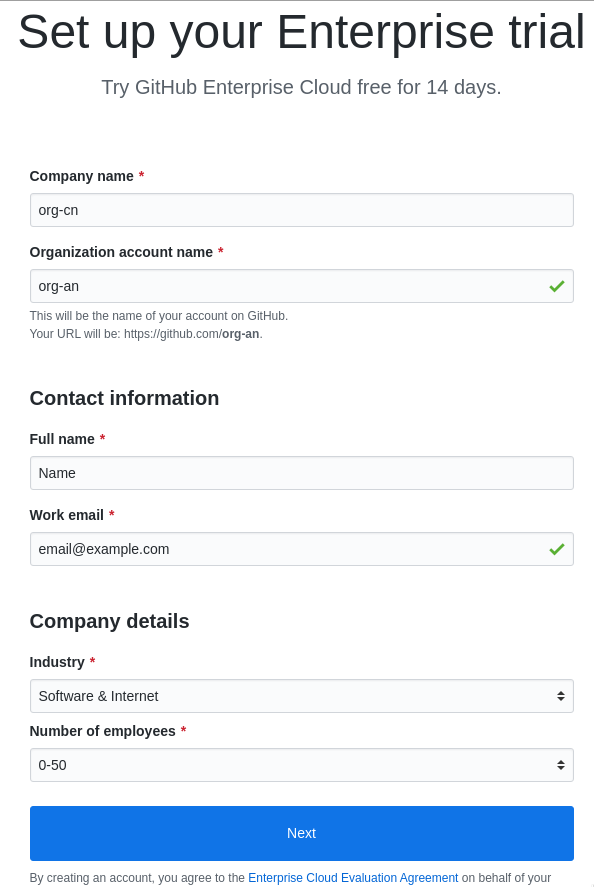
Click on the Trial, create the new organization:
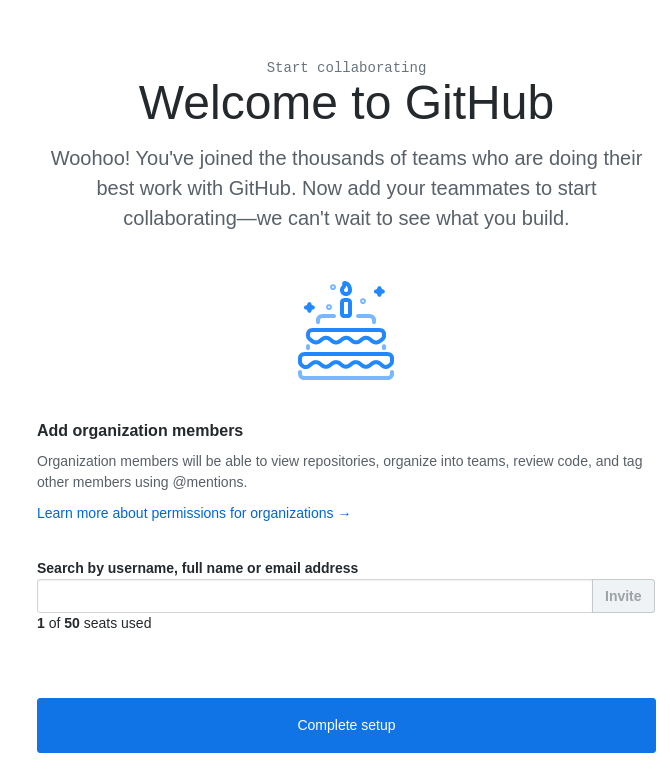
Can add users from here:
Now my user, which was used during the organization’s creation, has access to three organizations – working, RTFM’s and the Testing, just created:
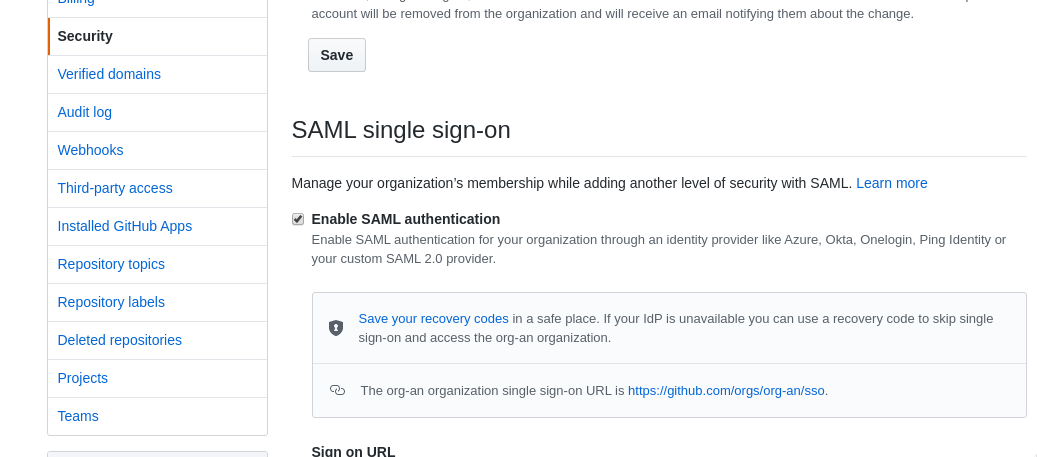
Now, go to the organization created Settings – Security, and you can see SAML available here:
Okta SAML – Github Enterprise Cloud – Organization configuration
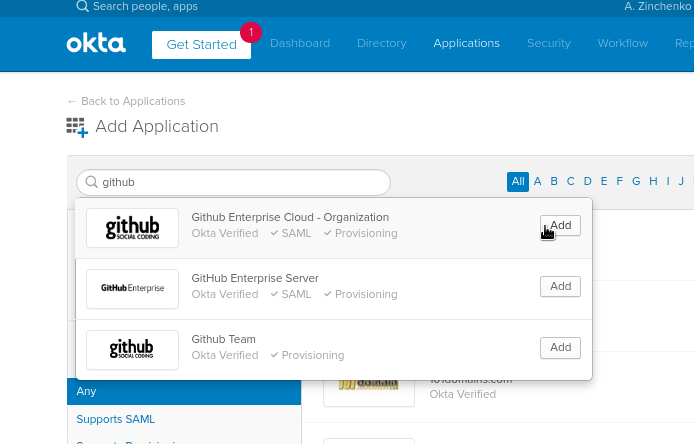
Go to the в Okta – Applications – Add application, find the Github Enterprise Cloud – Organization:
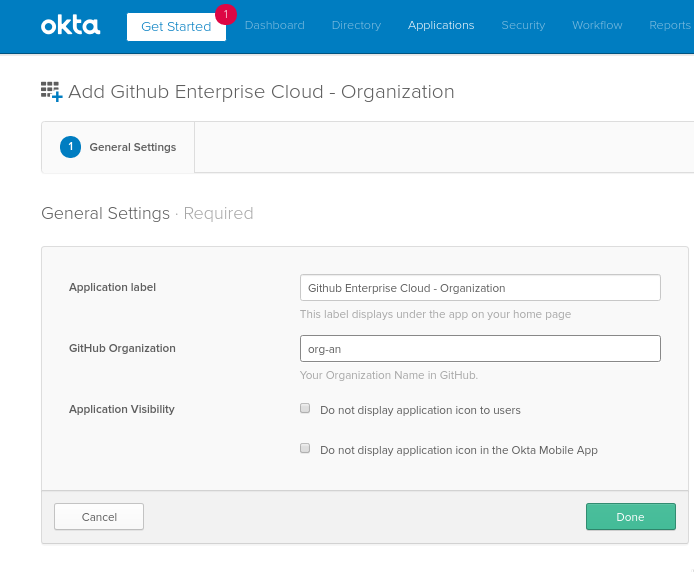
Set the organization name in the same view as it is in the Github:
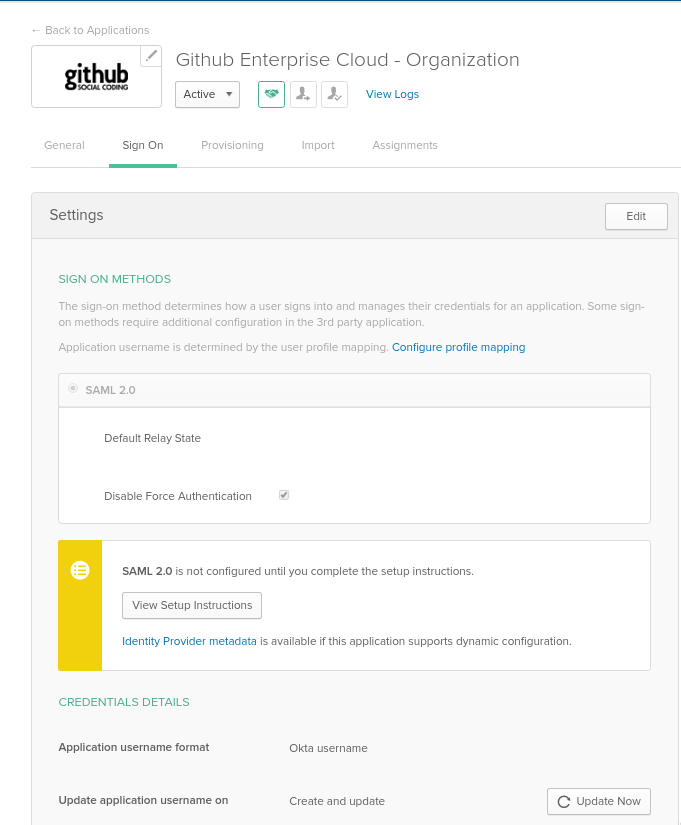
Go to the Sign On tab:
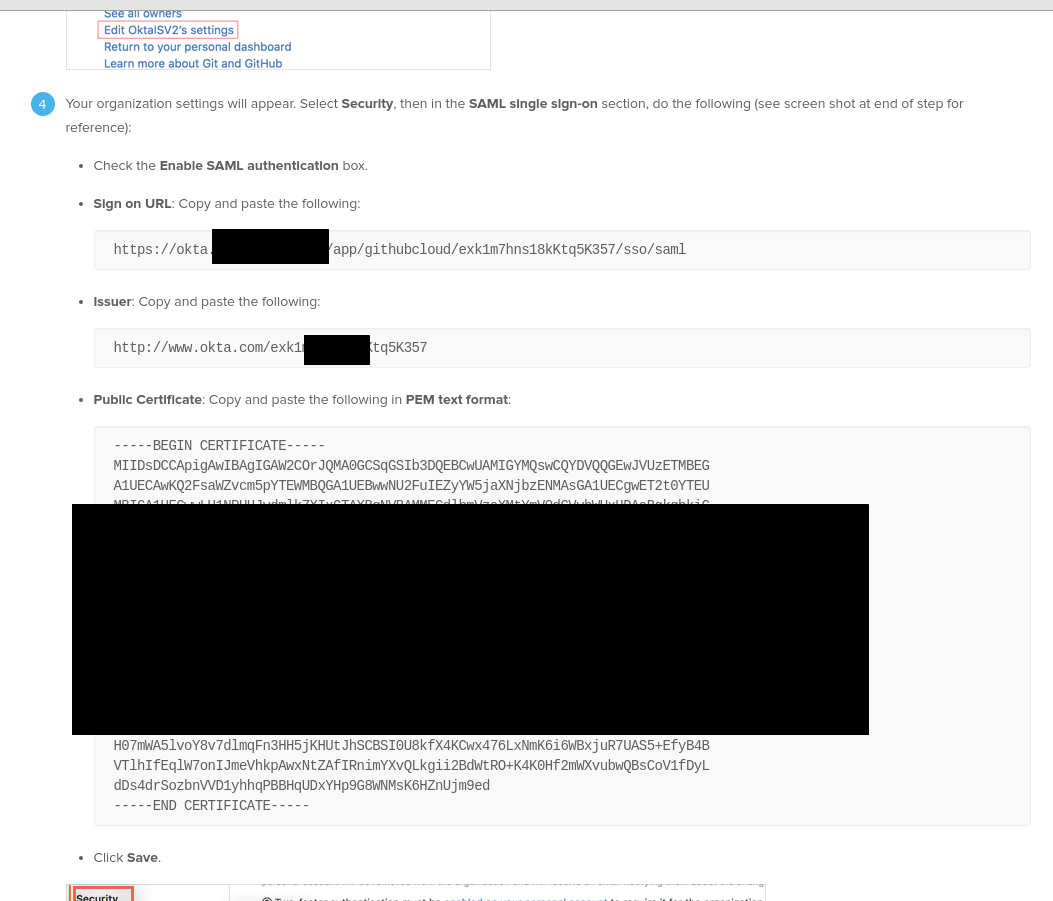
Click on the View Setup Instructions – you’ll be redirected to a page with already defined settings for your SAML:
SAML configuration in the Github Organization
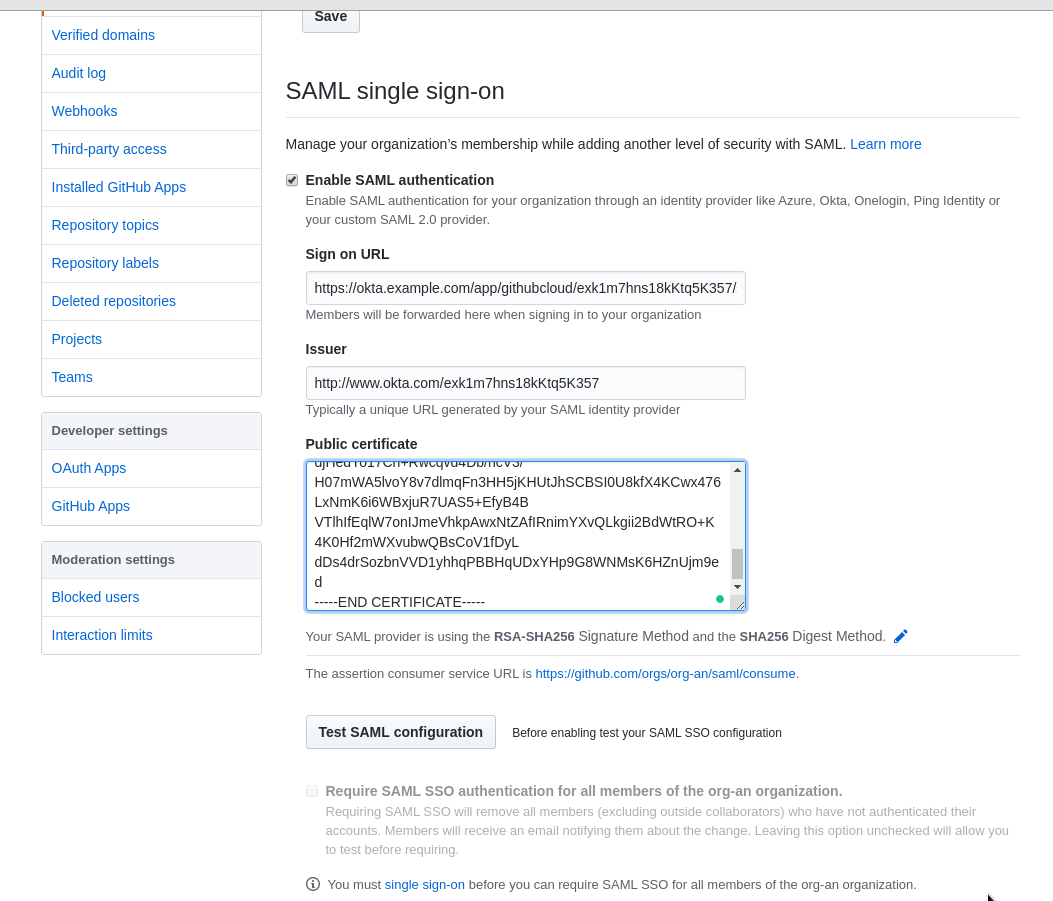
Go to the Github, click on the Enable SAML authentication, fill the fields with the data from the View Setup Instructions page, here is just three fields to copy-past:
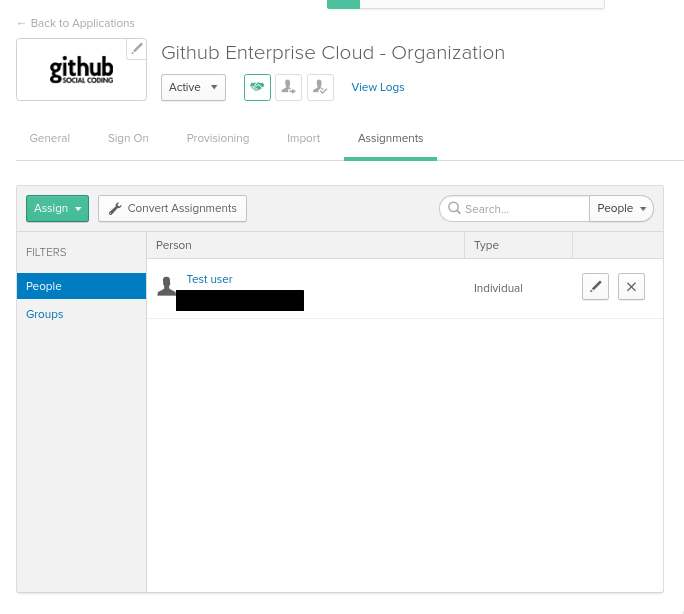
Go back to the Github application in the Okta, switch to the Assignments tab and assign a user:
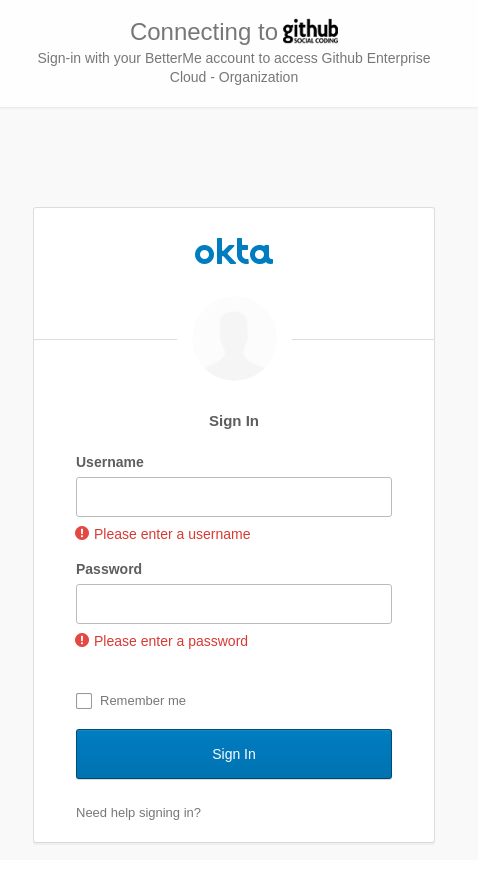
In the Github click on the Test SAML configuration: – you’ll be redirected to the Okta to authenticate:
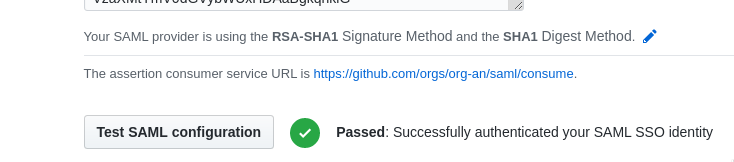
Log in with the Test user – test passed:
Do not forget to press the Save on the bottom.
SAML checking
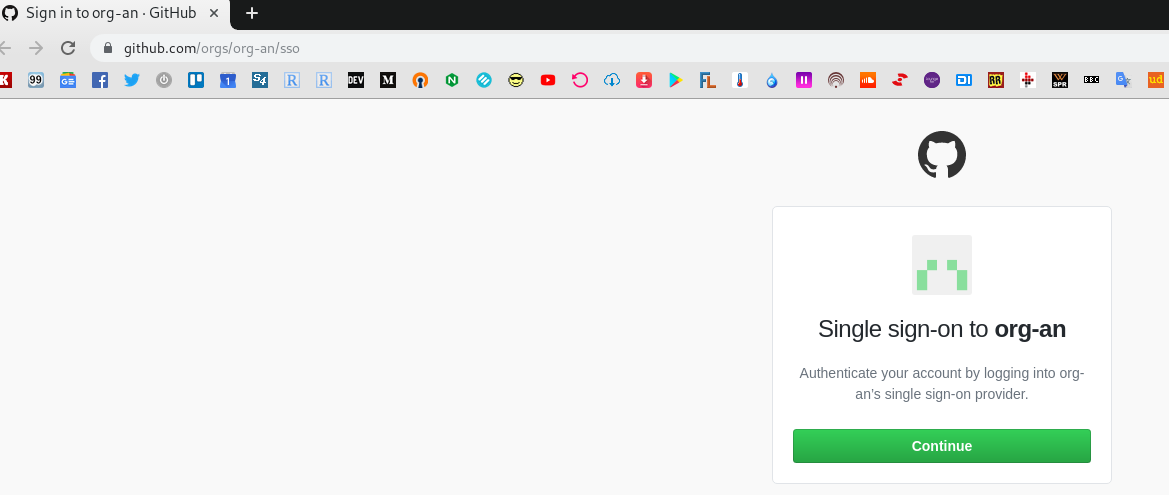
Find your SSO URL:
Open it in an Incognito:
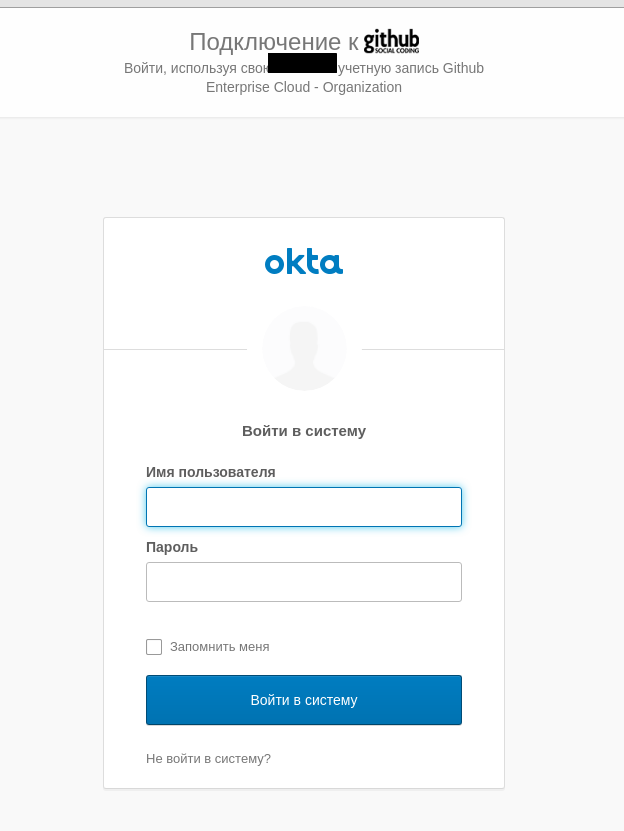
Click the Continue button – must be redirected to the Okta:
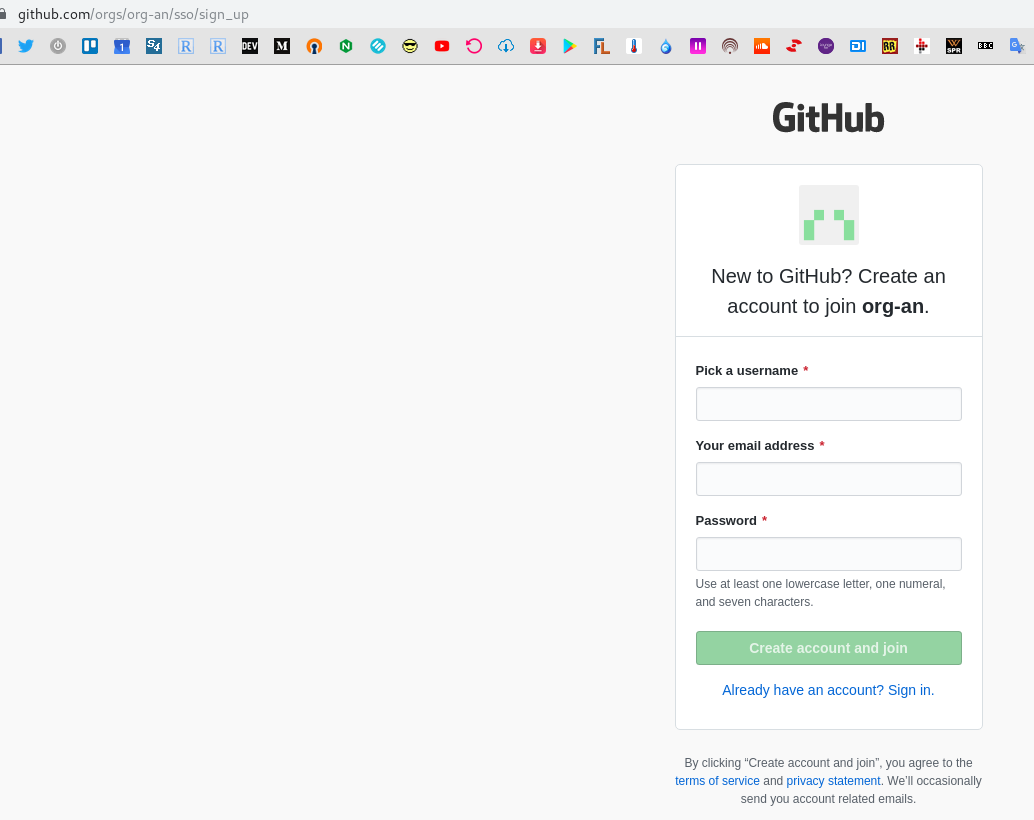
Here you can or create a new Github’s user – or log in with an already existing one.
In any case – Okta will use Just In Time (JIT) Provisioning to add this user to the Github’s organization:
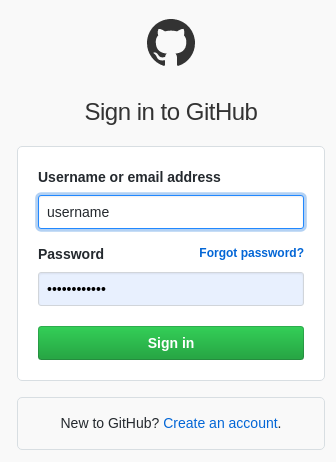
Log in:
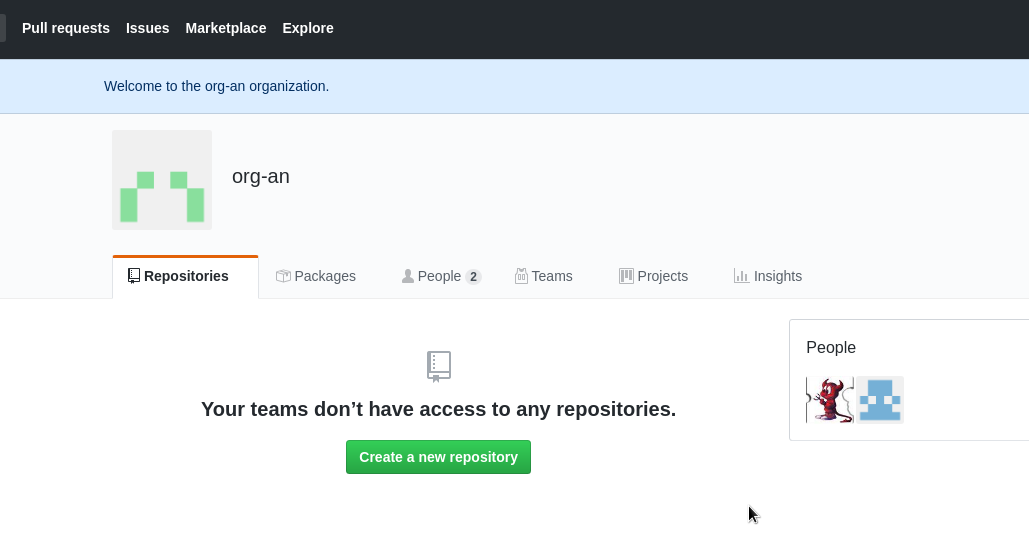
And now you are able to see the organization’s data:
Done.
Need to find out how to deal with groups now.
![]()